With the inception of cloud adoption, the requirements of digital businesses have increased significantly, making traditional identity tools and processes obsolete. The high complexity and cost of managing and operating legacy, on-premise IAM programs have boosted the need to migrate to cloud IAM architecture.
A strong Identity and Access Management (IAM) strategy has become essential for an effective cloud migration as it provides a cost-effective, agile, and highly scalable integrated access solution that helps enable new authentication methods.
However, moving the IAM system from well-established on-premise platforms to cloud-based alternatives is quite challenging for many organizations.
Security teams often struggle to define the right cloud IAM strategy that enables business agility and robust digital experience, all the while considering legacy architecture constraints and stringent compliance requirements.
Here are some identity and access management best practices that help you create a secure cloud environment.
Top 8 Cloud IAM Best Practices
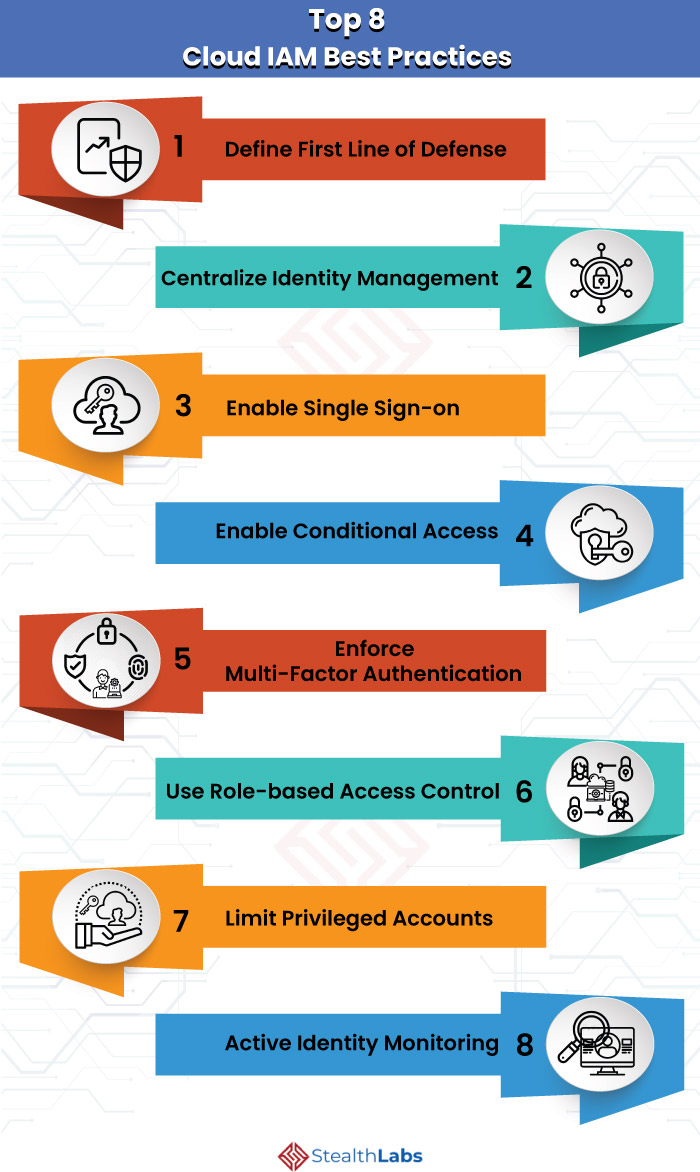
1) Define the First Line of Defense
With cloud and BYOD devices, users can access information anytime and anywhere. This has made network perimeters more porous, and the perimeter defense can’t be as effective as it was before.
Organizations must treat ‘identity verification at the user level’ as the first line of defense. Therefore, center your security controls and detections around user and service identities.
2) Centralize Identity Management
In a hybrid identity scenario, organizations must integrate their on-premise and cloud directories. With this integration, the security teams can manage accounts from one location, irrespective of where the account is created. It also enables users to access both cloud and on-premise resources with a common identity.
3) Enable Single Sign-on
Organizations should enable Single Sign-On (SSO) to apps, services, and devices from anywhere so that users can use the same set of login credentials to access the resources located on-premises or in the cloud. You can achieve SSO by using the same identity solution for all the applications and resources.
4) Enable Conditional Access
Users can access the organization’s resources by using various devices and applications from any location. Hence, the security team must ensure that these devices meet security and compliance standards.
But focusing on access control is not enough to balance security and productivity. You must know how to access a resource before you decide on access control. Turning on conditional access can address this requirement.
Conditional access helps you make automated access control decisions based on conditions for accessing the on-premise or cloud resources.
5) Enforce Multi-Factor Authentication
Organizations must enforce multi-factor authentication for all their users, including administrators and other privileged users, who can be impacted significantly if their account is compromised. Organizations that fail to implement extra layers of identity protection, such as MFA, are more susceptible to credential theft attacks.
6) Use Role-based Access Control
Access management for cloud resources is essential for any enterprise that adopted the cloud. Role-based access control helps manage user access to cloud resources, what they can do with the resources, and what areas they have access to.
Segregate users and provide only the amount of access they need to perform their jobs. Instead of granting unrestricted permissions, allow only specific actions at a particular scope.
7) Limit Privileged Accounts
Privileged Access Management is imperative for organizations to secure their critical assets and prevent data breaches.
Limiting the number of users having access to critical information or resources significantly reduces the attack surface.
To secure privileged accounts, organizations must isolate the accounts and systems from the risk of being exposed to cybercriminals. Implement ‘just in time’ access to further decrease the risk or exposure of privileges and increase visibility into the use of privileged accounts.
8) Active Identity Monitoring
Actively monitoring identities can help organizations quickly detect suspicious activities and trigger an alert to prevent the threat. Failing to monitor identity systems regularly can put you at risk of user credentials being compromised.
Organizations must implement monitoring methods to identify:
- Sign-in attempts without being traced
- Sign-in attempts from multiple locations
- Sign-ins from compromised or infected devices
- Suspicious IP addresses
StealthLabs As Your Cloud IAM Solution
StealthLabs Cloud Identity and Access Management solutions and services facilitate a smooth IAM program transformation by helping your organization define, deploy, and operate the right cloud IAM strategy.
Our identity and security experts help you tackle various cloud IAM projects, identify roadblocks, and architect and manage solutions that set you for cloud success.
Headquartered in Texas, StealthLabs is a global information security consulting service provider, catering to business needs in various US states and cities.
More IAM Articles:

