The demand for secure access has skyrocketed in recent years.
The businesses should meet the access demands of a diverse landscape of users across numerous, disparate applications while ensuring adequate cybersecurity.
However, slight mismanagement of the user credentials may lead to unprecedented security threats.
According to a recent Verizon Data Breach Report, 81% of the confirmed data breaches involved leveraging weak, stolen and default user passwords.
Whether it is passwords or email addresses, user information can quickly become a complex issue to track without a proper control system.
With the enormous amount of data to be stored, processed, and transmitted, many scenarios that require modifications to access permissions arise daily.
Meeting these demands across a wide variety of on-premise and cloud applications requires reliable and flexible access control solutions.
This is where Identity and Access Management (IAM) comes into play.
Defining Identity and Access Management (IAM)

IAM consists of processes, policies, and systems that manage the users’ digital identities in a secure, streamlined manner.
It encompasses various technologies such as Single Sign-On (SSO), profile management, Multi-Factor Authentication (MFA), and password management.
Identity and access management incorporates three significant concepts, identification, authentication, and authorization, which collectively ensure that the right users have the proper access.
Thus, IAM solutions have become a crucial component of IT security.
According to a recent survey by KPMG, 92% of businesses plan to increase their investments in identity and access management tools in the coming years.
IAM solutions are beneficial not only for users and security admins but also for enterprises as a whole.
While an effective IAM solution helps enterprises secure efficient access to technology resources across diverse systems, it also delivers many essential benefits.
6 Key Benefits of Identity and Access Management (IAM)
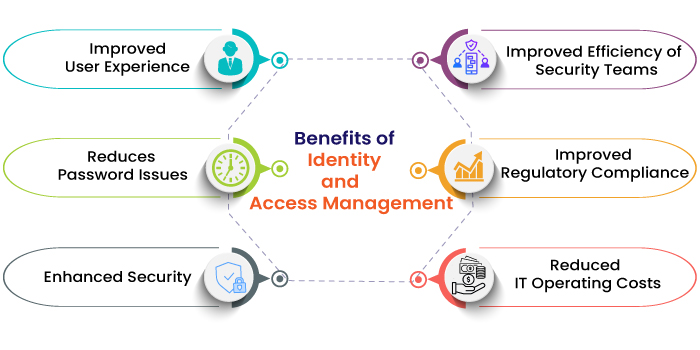
1) Improved User Experience
With the implementation of IAM tools, IT admins can create a unique digital identity for every user that includes a set of credentials. This eliminates the herculean task of the users to manage dozens of accounts for various corporate applications or resources.
With IAM systems, the end-users can access corporate networks, regardless of location, time, and device.
Moreover, the SSO method enables the users to access cloud-based, SaaS, web-based and virtual applications with their unique identities.
2) Reduces Password Issues
Apart from enabling easier sign-in processes, IAM solutions prevent many password-related issues such as managing passwords in excel or on sticky notes and forgetting user credentials.
The IAM tools offer password management features that help security admins implement password best practices, such as frequent password updates and strong authentication measures including MFA, biometrics, or role-based access.
3) Enhanced Security
IAM solutions help businesses implement adequate security policies across all systems, platforms, applications, and devices. This makes it easier to identify security violations, remove inappropriate access privileges and revoke access whenever needed.
With IAM systems, employees can access the systems depending on their specific role and cannot escalate privileges without approval or a role change. This, in turn, significantly limits the potential insider security threats.
4) Improved Efficiency of Security Teams
In addition to improving the security posture, the most significant benefit of IAM is improving the efficiency and effectiveness of security teams.
With the help of IAM tools, the security admins can grant access rights based on the principle of least privilege to user roles. This ensures that users, including clients, employees, contractors, third-party vendors, and partners, can be quickly and efficiently organized with only the right access.
Moreover, IAM systems use automation, AI, and machine learning that helps administrators to automate many critical aspects of managing identities, authentication, and authorization.
5) Improved Regulatory Compliance
Government data regulations such as CCPA, HIPAA, and GDPR make organizations accountable for controlling access to customer and employee information. The regulations have data security, privacy, and protection mandates such as who has access to the information and how the access is protected, which are directly related to IAM. Thus, IAM solutions help enterprises meet regulatory compliance and industry best security practice standards.
6) Reduced IT Operating Costs
According to a recent survey, 30-50% of help desk calls are for password resets. And, on an average, a password reset costs an organization around USD 70.
IAM solutions help the organization save these costs by minimizing the time needed to deal with user account-related issues.
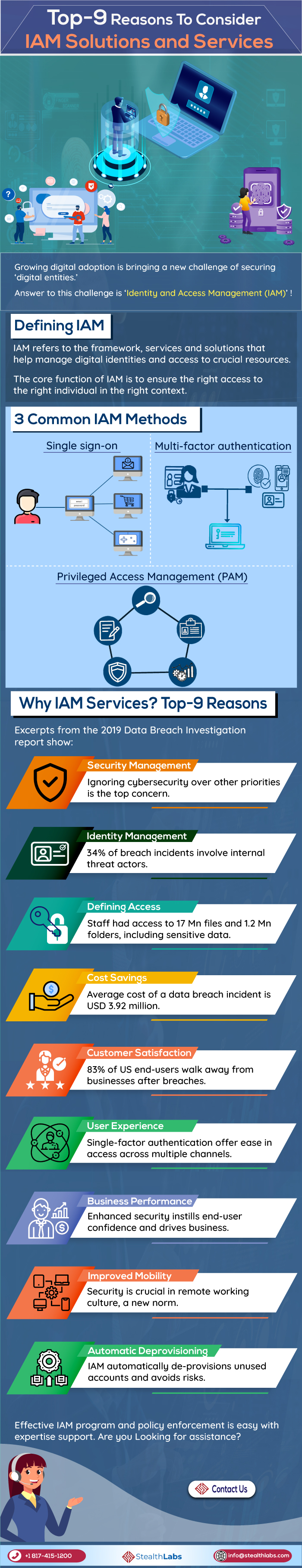
ALSO READ – Infographic: Top-9 Reasons To Consider IAM Solutions and Services
How IAM Helps?
Ensuring the right access to the right individual at the right time in the proper context of the enterprise is the sole idea of the Identity and Access Management (IAM) services.
Whether it’s for external parties like end-users or business partners or internal parties like internal staff or contractors, IAM services offer a dedicated digital entity, as a combination of roles and privileges for every individual user.
The three most common IAM methods are:
- Single sign-on, where there will be unique sign-on credentials for access to any system, network, or service.
- Multi-factor authentication involves two or more forms of login credentials for information access, in combinations of password and a biometric tool, biometric and pin, and password and call/text-based authentication.
- Privileged Access Management (PAM), where user access is bound to a set of privileges. This is considered the most secure way, with more visibility, monitoring, and access control.
In these most common ways, IAM services offer high-level security to organizations’ systems and data.
9 reasons to consider IAM services:
1) Security Management

A data breach incident is the most common concern to every organization today, irrespective of size and market position. One of the 2019 Data Breach Investigation reports mentions that more than 40 percent of such incidents involved small businesses. Ignoring cybersecurity over other business priorities is cited as the top reason. Hence, you need robust IAM services to secure your organization from internal and external threats.
IAM services ensure overall security by providing necessary controls in place.
2) Identity Management

The same report found ‘internal threat actors’ as the key reason behind 34 percent of breach incidents. A large portion of data breaches, caused by internal threats, involves privilege misuse and manual errors.
Having an IAM system in place helps you gain full access control and offer access privileges only to the right person under the right context. This protects from external threat actors in case your internal member falls prey to a threat attempt.
3) Defining Access

Defining access is one crucial aspect that can lead to potential losses if dealt with improperly. As per the report findings, every employee had access to 17 million files and 1.2 million folders, with the majority of them enjoying access to sensitive files. This is purely tied to how the organization defines access among its teams.
Any employee might not require access to everything around and be limited to his/her core functioning.
Mishandling this act of defining access can cause many troubles pertaining to information security in the future. IAM services ensure the right segregation of tasks and align employees and access to them strategically.
4) Cost Savings

If you think spending on cybersecurity is expensive, then consider how much a data breach incident can cost your organization. The average cost of a data breach can be around USD 3.92 million, shows a renowned Cost of Data Breach report. So, implementing an IAM system and tools can save such unnecessary costs, alongside addressing your cybersecurity needs.
5) Customer Satisfaction

One of the leading data breach surveys confirms that 83 percent of US customers prefer staying away from businesses after a breach incident, and more than 20 percent don’t want to come back ever. So, ensuring data security is key to gaining user trust and retaining customers.
An IAM system provides that user data is safe and secure across all channels by offering different layers of security across multiple platforms.
6) User Experience

Options like single-factor authentication offer ease in access across multiple channels, mainly social media logins. As users find numerous ways to share their content, enhanced experience and security assurance are advantageous.
Single-factor authentication helps users login to multiple platforms and keeps their job of content sharing uninterrupted from every-time logouts.
7) Business Performance

Attracting more customers through enhanced user experience and enhanced security is the best way to drive business performance. Thinking how IAM helps here? By alleviating your security concerns, IAM services and solutions help you focus on other aspects of business growth and pressing matters.
Defining access to employees in a large enterprise setup is no more cumbersome with IAM services, which can ensure login for hundreds of employees with ease in a secure environment. Moreover, a robust IAM system allows your IT teams to explore other focus areas.
8) Improved Mobility

The COVID-19 crisis gave rise to the remote working culture, which is now a new normal for most companies. But ensuring security from threat actors is crucial as employees operate on different networks outside the organizational purview. So, it’s essential to ensure security in mobile operations for employee safety and corporate data against internal and external threats.
9) Automatic Deprovisioning

Unused or abandoned accounts lay down the path for intruders to gain unauthorized access. IAM tools take a strategic approach by automatically de-provisioning unused accounts, thus avoiding the possibility of such attacks. This may not require the attention of your IT teams.
Identity and Access Management Solutions [Infographic]
In Conclusion
With the increasing complexity of data breaches, the scope and scale of IAM will continue to witness steady growth.
As per the market report by Grand View Research, the IAM market is estimated to reach USD 24.12 billion by 2025, at a CAGR of 13.1%.

Wait No More! Implement IAM Solutions Now!
Need Support? Contact Stealthlabs!
Stealthlabs is a US-based Identity Management (IDM) Service Provider with strong domain expertise and excellence in approach. Our portfolio of IDM services includes Access Management, Identity Governance and Data Governance.

