In the present-day ever-evolving cybersecurity landscape, every organization, regardless of size, nature, and industry, are at the risk of cyberattack.
When a cyber incident occurs, it can quickly escalate to a business crisis, leading to financial losses, legal implications, operational disruption, and reputational damage.
Despite these severe consequences, the vast majority of organizations are still unprepared to appropriately respond to cybersecurity incidents. In fact, according to a recent study by IBM, 77% of the surveyed organizations do not have a Computer Security Incident Response Plan (CSIRP) applied consistently across their enterprise.
As cyber-attacks increasingly take a toll on business operations and reputation, developing a robust Cyber Incident Response Plan becomes essential for organizations to stay ahead of the cybersecurity curve.
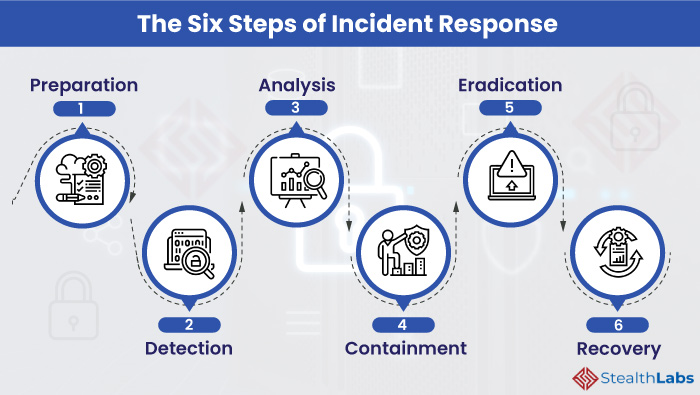
Here are six crucial steps that every IR plan should cover to effectively address the inevitable security incidents:
The Six Steps of a Cyber Incident Response Plan
Organizations must develop a proactive and responsive set of capabilities as part of their incident response plan to rapidly adapt and respond to cyber incidents.
Proactive Capabilities
- Preparation
- Detection
- Analysis
Responsive Capabilities
- Containment
- Eradication
- Recovery
1) Preparation
Preparation is crucial to effective incident response. Even the best Cyber Security Incident Response Team (CSIRT) cannot effectively respond to an incident without predetermined instructions. Preparedness involves:
- Design, development, training, and implementation of enterprise-wide IR plan
- Creating communication guidelines to enable seamless communication during and after an incident
- Conducting cyber simulation exercises to evaluate the effectiveness of incident response plan
2) Detection
The objective of this phase is to monitor networks and systems to detect, alert, and report on potential security incidents.
- Adopt cyber threat intelligence (CTI) capabilities to develop a comprehensive cyber monitoring program and to support ongoing monitoring and detection
- Conduct cyber compromise assessments to detect unknown compromises
3) Analysis
The majority portion of the efforts to properly understand the security incident take place during this step. It involves:
- Gathering information and then prioritizing individual incidents and steps for a response.
- Forensic preservation and analysis of data to determine the extent and impact of the incident.
During the event of an incident, the incident response team should focus on three areas:
- Endpoint Analysis
- Determine tracks left behind by the malicious actor.
- Analyze a bit-for-bit copy of systems to determine what occurred on a device during the incident.
- Binary Analysis
- Analyze malicious tools or binaries used by the malicious actor and document the functionalities of those programs. The analysis can be performed through Behaviour Analysis or Static Analysis.
- Enterprise Hunting
- Analyze existing systems and event logs to determine the scope of the incident.
- Document all the compromised systems, devices, and accounts.
4) Containment
This is the most critical stage of incident response. The strategy for containing an incident is based on the intelligence and indicators of compromise gathered during the analysis phase. The security team should focus on taking risk-mitigating actions to prevent further impact and damage to the organization.
- Coordinated Shutdown: Once identifying the compromised systems, perform a coordinated shutdown of these devices. The IR team should be instructed to ensure proper timing.
- Wipe and Rebuild: Wipe the compromised systems and rebuild the operating systems from scratch. Change the login credentials of all the compromised accounts.
5) Eradication
Once you have identified domains or IP addresses leveraged by the malicious actors for command and control, issue ‘threat mitigation requests’ to block the communication from all channels connected to these domains. The IR team should remove the known existing threats from the networks.
6) Recovery
- Develop a near-term remediation strategy and roadmap
- Focus on resuming normal business operations
- Develop a long-term risk mitigation strategy
- Document the incident to improve the IR plan and update security measures to avoid such incidents in future
7 Tips to Build a Cyber Incident Response Plan
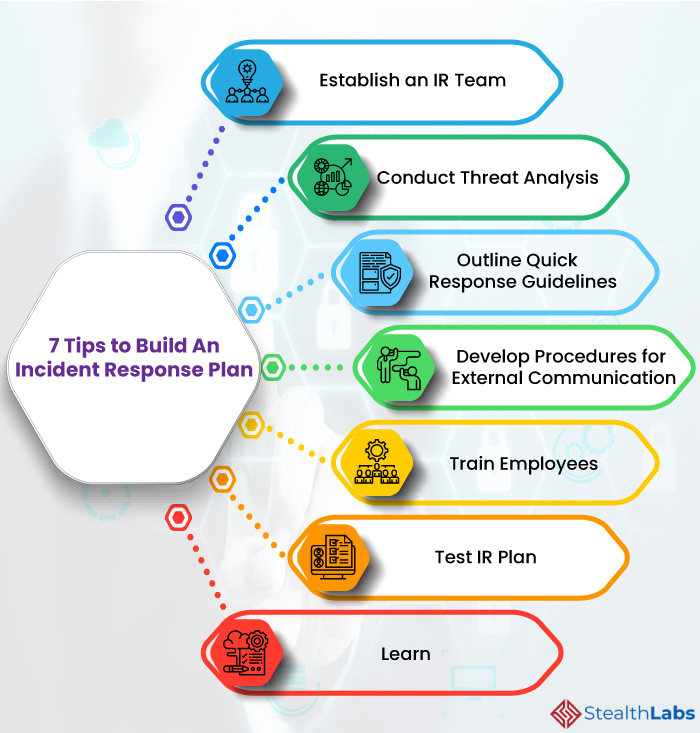
1) Establish an IR Team
Form an incident response team and clearly define each team member’s roles and responsibilities to ensure a proper and consistent response to threats. There are various types of IR teams, including internal, external, or a mixture of both.
The IR team should comprise experts in breach management, threat intelligence, malware analysis, forensics, and incident detection.
The IR team analyzes security breaches and threat intelligence reports to help develop the organization-wide incident response strategy.
2) Conduct Threat Analysis
Determine what criteria, a specific security issue, an attempted attack, or a cumulative set of circumstances, is defined as a security incident.
Once defined, conduct an incident threat analysis to baseline and benchmark your current readiness to respond and identify incidents. Then, make the necessary improvements to your organization’s current security measures.
3) Outline Quick Response Guidelines
Based on the incident threat analysis, develop a quick-response guidebook for the most common security incidents. This will help the IR team to respond promptly to the most common attacks that threaten your organization.
Moreover, outline step-by-step procedures and processes for making critical incident response decisions and define who will be responsible for these decisions.
4) Develop Procedures for External Communication
Communicating with your partners, customers, and investors during an incident plays a critical role in maintaining customer trust and brand reputation.
Around 35% of customers reportedly gain trust in an organization if they are appropriately informed about a breach.
Therefore, ensure to document communication procedures to notify potential customers and stakeholders about the incident. It is also beneficial to communicate with external breach responders and other experts to receive further guidance for handling the incident.
5) Train Employees
Employees of your organization are an essential component of a cyber incident response plan. Ensure that all employees are aware of the IR plan and have access to it. Moreover, train them to understand their roles and carry out their responsibilities during an event.
6) Test IR Plan
Comprehensive cybersecurity relies on a well-practiced and rehearsed incident response plan. So, organizations must conduct regular ‘fire drills’ that stimulate a cyber incident to identify any weak links in the response plan. Then, ensure to refine the response plan based on the feedback from the ‘fire drill.’ Moreover, the incident response plan should be tested for various scenarios.
7) Learn
Learning from past incidents is imperative for organizations to build a secure, vigilant, and resilient business environment. Meet all the teams and employees who handled a previous incident to discuss what went well and what needs to be improved. Document the incident and update the IR plan and security measures to avoid similar incidents in the future.
In Conclusion
As the cyber threat environment continues to evolve rapidly, preparing for the inevitable cyber incident involves more than preparing to react. It involves the ability to respond effectively and recover thoroughly.
Therefore, merely having a cyber incident response plan is not enough. The security team must understand the plan and test it across the organization, including among business leaders.
StealthLabs Can Help You!

StealtLabs’ Cybersecurity Incident Response Services will provide your organization with a cross-functional approach for improved communication across your business for a faster, more efficient, coordinated, and reliable breach response.
Headquartered in Texas, StealthLabs is one of the leading Information Security Service providers in the US market. With years of industry presence and strong domain expertise, we have been catering to business needs across various US states and cities.
More Cybersecurity Articles :